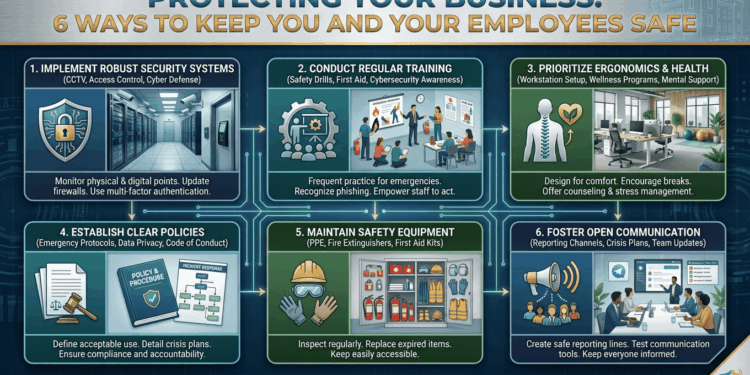
In today’s business world, keeping your company and employees safe has gotten more complicated than ever before. You’re not just dealing with physical security concerns anymore, sophisticated cyber attacks can compromise your operations and sensitive data in ways that weren’t even possible a decade ago. Sure, locking up at night is still important, but it’s just one piece of a much larger puzzle. When you create a comprehensive safety strategy, you’re doing more than protecting assets; you’re showing your team that their well-being matters, which naturally boosts morale and productivity. As businesses become increasingly interconnected, a multi-layered approach to security isn’t just nice to have, it’s absolutely essential for long-term success.
Implement Comprehensive Physical Security Measures
Your physical workspace deserves serious attention when it comes to security. Start with a detailed walk-through of your premises, looking for vulnerabilities like unsecured doors, dimly lit corners, or areas your cameras can’t reach. High-quality surveillance systems work double duty, they discourage potential threats and give you valuable footage if something does happen. Access control systems (think keycard entry or biometric scanners) let you control who gets in while creating a digital record of movement throughout your building. Don’t forget about regular maintenance checks on alarm systems, fire suppression equipment, and emergency exits, these features need to work flawlessly when emergencies strike. Establishing clear visitor protocols and requiring ID badges for everyone creates accountability and makes spotting unauthorized individuals much easier.
Develop and Enforce Robust Cybersecurity Protocols
Digital threats are some of the most dangerous challenges businesses face today, which makes strong cybersecurity absolutely non-negotiable. Start with password policies that require complexity and regular updates, then layer on multi-factor authentication for all critical systems. Keeping software updated and patches current closes security gaps that hackers love to exploit. Enterprise-grade firewalls, quality antivirus software, and intrusion detection systems create multiple barriers against cyber attacks. Your employees need training to spot phishing attempts and social engineering tactics, they’re your first line of defense. Secure protocols for handling sensitive information, including encryption and secure file-sharing practices, protect both your company’s data and your customers’ trust.
Create and Maintain Emergency Response Plans
How your business responds to emergencies can determine whether you face a manageable situation or a complete disaster. You need detailed emergency response plans covering everything from natural disasters and medical crises to active threats and evacuations. Regular drills help ensure everyone knows exactly what to do, when crisis hits, you want automatic responses, not confusion. Clear communication protocols matter tremendously, so establish systems that can quickly reach all staff members during emergencies.
Establish Comprehensive Employee Verification and Monitoring
Protecting against internal threats requires careful attention to who you hire and ongoing vigilance about account activities. Thorough background checks for new employees, including credential verification, employment history, and appropriate criminal background screenings, establish a foundation of trust. Regular audits of user permissions ensure employees only access the systems and data they actually need for their jobs. Watching for unusual patterns, like login attempts at strange hours or from unexpected locations, helps you catch compromised credentials before real damage occurs. When protecting sensitive business systems and customer data, professionals who need to detect and prevent unauthorized account access rely on account takeover protection to safeguard against both external hackers and internal bad actors. Clear policies about account sharing, password management, and reporting suspicious activities build a security-conscious culture throughout your organization.
Invest in Employee Safety Training and Awareness Programs
When you properly train your workforce, they transform from potential weak points into active defenders of your business security. Regular training sessions should cover workplace safety protocols, emergency procedures, cybersecurity practices, and threat recognition, both physical and digital. Make your training engaging and interactive, using real-world examples that connect with your specific industry and work environment. Encourage open communication so employees feel comfortable reporting concerns or suspicious activities without worrying about negative consequences. A security awareness program with regular threat updates keeps everyone alert and informed. When you recognize and reward employees who demonstrate excellent safety practices or identify potential issues, you reinforce these behaviors and encourage continued vigilance across your team.
Maintain Robust Data Backup and Recovery Systems
Protecting your operations against data loss, whether from cyber attacks, equipment failures, or disasters, requires solid backup and recovery strategies. Automated backup systems should regularly capture critical business data, customer information, and operational records to minimize loss during incidents. Using both on-site and cloud-based solutions protects against local disasters while giving you quick recovery options when you need them. Testing your backup systems and recovery procedures regularly verifies that you can actually restore data and meet your business continuity timelines.
Conclusion
Creating a secure business environment takes ongoing commitment, investment, and vigilance across multiple protection areas. These six comprehensive strategies can significantly reduce your vulnerability to both physical and digital threats while building a safer workplace for your team. Modern business operations are interconnected, which means your security measures need to evolve continuously as new threats emerge and circumstances change. Regular assessment and updates keep your protocols effective and aligned with your organization’s growth. Business security isn’t a project you complete and forget about, it’s an ongoing process requiring dedication, resources, and active participation from everyone in your organization to maintain truly effective protection.